The cybersecurity threat landscape has changed, and nothing reveals that truth more clearly than the growing severity of the ransomware threat facing businesses worldwide.
Gone are the days of disruptive email worms and viruses created by hobbyists to wreak havoc in computer systems. Today, a for-profit motive has replaced many of the other reasons that once drove the creation of flavors of malware. With ransomware attacks splashing into global headlines due to service disruptions at critical infrastructure points and in large-scale processing and manufacturing, it is a threat that no business can afford to ignore.
What is ransomware, and why should your business have an active anti-ransomware policy in place? Where do these threats come from, and what can you do to mitigate these pressing concerns? Investigate this issue with us to understand the problem, its potential solutions, and what the future holds.
What Is Ransomware?
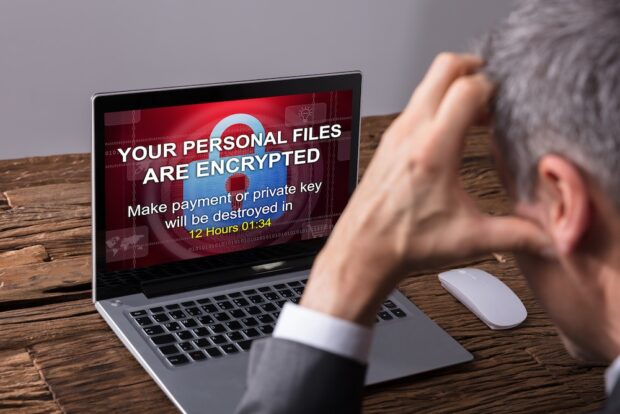
Ransomware is a specific type of malware that holds critical computer systems and the data they contain for ransom. There are many possible attack vectors for ransomware programs to use. Some have exploited weaknesses at the operating system level, while others rely on software exploits or human error to introduce their payloads onto vulnerable systems.
Once ransomware infects a computer, it uses an unbreakable encryption algorithm to lock down the entire system. More advanced ransomware may also scan open network ports and spread to other machines on the same network, potentially encrypting dozens or even hundreds of hard drives and servers. Once their machine is locked down, the user sees a ransom note demanding payment in cryptocurrency, such as Bitcoin, in exchange for a tool that will let them decrypt their data.
Naturally, the bigger the target, the larger the potential ransom payment. Ransomware initially targeted individual users but quickly transformed into extortion on a global stage. In May 2024, the Colonial Pipeline system sustained a ransomware attack that shut down critical systems managing the flow of refined gasoline to parts of the US. According to news reports, the company paid a ransom of $5 million.
The US government later recovered some of those funds, but Colonial faced days of severe service disruptions compounded by an unlocking tool that worked slowly and poorly. Colonial is far from the only high-profile example with ransoms paid in the millions.

Which Factors Influence A Company’s Ransomware Risk?
Are you a target of ransomware just by being a business owner? Not necessarily, although no business faces zero risks. There are several factors that influence the way ransomware gangs target their attacks, and not all of them are within a company’s control. Some of these factors include:
- The size of the business, in both personnel, revenue, and profit
- How ‘online’ the business is, i.e. how connected its systems are and which software or tools are in use
- The company’s security footing. Some businesses are easier targets than others due to a lack of basic digital safeguards.
- Anti-malware training for employees. Do the staff know the risky behaviors and red flags to avoid?
Ultimately, training and preparation are the best ways to reduce the risks that you may face from ransomware.

Avoid These Problematic Online Activities In The Workplace
An employee could easily open the door for ransomware to infect their machine without meaning to make a critical mistake. Training staff to avoid online behaviors that increase the risk of such events is worth the investment of time and money. Let’s consider a few of the behaviors to eliminate:
- Opening any email attachments from unknown or unverified senders, especially when the user did not expect any communication
- Downloading and installing illicit or unknown software outside of the IT department’s approved procedures
- Securing networks poorly or leaving highly privileged and unused user accounts active on your computer systems

How Secure Are Your Digital Document Procedures?
While some of the biggest ransomware attacks occur through the exploitation of computer vulnerabilities, there are other ways for malicious payloads to make their way inside your business. In ‘spear phishing’ attacks, seemingly legitimate emails target employees of the company with phony email attachments.
Imagine that an important manager in the business receives an email that purports to be from a supplier seeking confirmation of the information contained in an attached PDF file. The user downloads and opens the file, only to discover that there are malicious macros in the file that run automatically and execute a ransomware payload. Suddenly, the business gets a serious problem.
The right tools can help mitigate these risks, just as better online behavior can help avoid infections. Kofax Power PDF, for example, has built-in security solutions that identify potentially malicious or malformed files and prevent them from opening. Combined with other security-enhancing features, it can form an integral component of enhanced document security solutions.
While safe online habits should be your first line of defense, make sure that your last line of defense is strong enough to protect your business.

Strategies For Mitigating Ransomware Risks
Along with providing staff with training and deploying strict firewalls and document security, there is another strategy that your business can adopt: preserving data integrity. By investing in off-site or offline backup solutions for all your critical data, recovery from a ransomware attack might not involve rebuilding from scratch or paying the ransom. Frequently, even daily, backups can provide the peace of mind of business continuity following any disaster—ransomware attack or otherwise.
Put Your Business On Guard Against Ransomware Today
The risks of ransomware are real, but they don’t mean that business owners should live in fear of threats. Properly training staff on appropriate safety techniques and pairing that training with software developed with security in mind can both help. With these measures, it’s possible to reduce these risks. Avoiding the red flags for ransomware, including phishing attacks and malformed digital documents, means less stressful workdays.
Review your policies today and consider what else your teams could do to keep ransomware at bay.
 Comeau Computing Tech Magazine 2024
Comeau Computing Tech Magazine 2024




